FAQs
Those might have popped-up in your mind.
Categories
Are SecureNT Root Certificates trusted by the browsers ?
Intranet SSL certificate’s root certificate chain is not trusted by default on popular browsers like Chrome, Edge, Internet Explorer, Safari, Firefox, etc. This means that unless certain steps are taken, a client PC will get a “certificate not trusted” error when a user uses a web browser to access a website hosted on a Server with Intranet SSL.
But these steps (installation of SecureNT CA root certificates) need to be taken once only. After those steps are taken, the client PC will always trust the Intranet SSL certificate.
You can find the steps here.
Tagged In
No Comments Yet.
Can you provide technical details of SecureNT Intranet SSL Certificates ?
-
Certificates are issued by default with RSA Encryption, 2048 bit Key Size, and Sha256 Hash Algorithm
-
The Root Certificate chain is from Secure Network Traffic
-
Custom Root Certificate chain on your organization name is available on request
-
Client Authentication Certificates for Single Sign-on and Document Management / Signing available on request.
-
RSA Certificates with different Key Size and Hash Algorithm available on request ECDSA Certificates with 256 and 384-bit Key Size also available on request
Tagged In
No Comments Yet.
How to Create CSR with SAN Values Using OpenSSL ?
For creating CSR with SAN values (X.509 v3 Extension) it’s important to create a configuration file with the required certificate details. Execute following command in openssl.
openssl req -newkey rsa:2048 -nodes -keyout pvtkey.cer -config config.cnf -out csr.txt -utf8It will create a Private key (pvtkey.cer) and CSR file (csr.txt).
Sample Configuration file (config.cnf)
[req]
prompt = no
distinguished_name = dn
req_extensions = ext
[dn]
CN = 192.168.2.23
O = Abc Corporation
L = Sydney
ST = New South Walse
C = AU
[ext]
subjectAltName = @alt_names
[alt_names]
IP.1 = 192.168.2.23
IP.2 = 10.12.4.112
DNS.1 = 192.168.2.23
DNS.2 = 10.12.4.112
DNS.3 = sms.abc.local
DNS.4 = localhostNote that you need to put City name against "L" (=Location), and 2 letter Country ISO code against "C" (=Country).
It will generate CSR with CN=192.168.2.23 and 3 SAN values: 10.12.4.112, sms.abc.local and localhost.
Notice that when IP address is there in CN or SAN, we need to put its value against both IP Address and DNS. For others (URL, Servername etc) only DNS value is required.
Tagged In
No Comments Yet.
How to create the CSR with SAN in Windows IIS ?
Following steps are applicable for all versions of IIS. Windows Server should be domain joined.
-
Open the MMC console and add the Certificate snap-in to it as Local Computer. Right Click Personal node on the left and Select All Tasks –>Advanced Operations –> Create Custom Request.
-
Choose Proceed without enrollment policy and Click Next. Choose No Template Legacy Key for compatibility reasons. Use PKCS#10.
-
Click Next and click Properties. Give a friendly name for the certificate and a description. Ensure that you hit Apply as soon as you are done with the tab.
-
Click on Subject tab and add all SAN values under “Alternative Name“. Under Subject Name, enter the Common Name (CN), Organizational Unit (OU), Organization (O), City (L), State (S), and 2 letter Country (C) code values. Click Apply.
-
Under the Extensions tab, expand Extended Key Usage (application policies) and select Server Authentication and Client Authentication. Click Apply.
-
Under the Private Key tab, set the Key size to 2048 (or 4096) under Key options. Tick Make Private Key exportable. Select Exchange as the Key type. Click Apply. Click OK.
-
Select a location to save the file. Choose the file format as Base 64. Click Finish.
CSR is generated with SAN values.
Tagged In
No Comments Yet.
How to deploy SSL Certificate in Windows Azure environment ?
Installation of SSL Certificate in Windows Azure environment is different. It requires a special password protected PFX file with Triple DES encryption. Please mention this requirement while placing request to us. We will send this special PFX file.
Installation steps are given on this Blog Post.
Tagged In
No Comments Yet.
How to generate correct CSR when IP address is in CN or SAN ?
When an internal/external IP Address is part of Common Name (CN) or Subject Alternative Name (SAN) care needs to be taken while generating the CSR.
If not done correctly then the latest browsers like Chrome and Edge give an error – “Your connection to this site is not secure.” Note that deprecated Microsoft Internet Explorer does not give any error in this case.
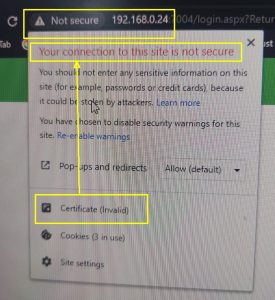
To avoid this problem please ensure that the IP address is mentioned in the SAN extension as DNS value and IP Address. For example, if CN=192.168.23.1 then the CSR should have 2 SAN values viz., DNS=192.168.23.1 and IP=192.168.23.1
If you wish to generate the CSR on Windows Server then read this FAQ. How to create the CSR with SAN in Windows IIS
If you wish to generate the CSR using OpenSSL then this link explains step-by-step how to generate the CSR using OpenSSL
Tagged In
No Comments Yet.
How to install Intranet SSL on Ubuntu Linux ?
If you asked for the Intranet SSL without CSR, you would have received server.pfx file on email.
-
Copy the server.pfx file to the Ubuntu machine
-
Ensure that openssl package is installed on Ubuntu
-
Run the following command: sudo openssl pkcs12 -in server.pfx -passin pass:inetssl2 -out serverpfx.pem -nodes This will create a serverpfx.pem file, which contains the issued certificate, two CA certificates and the private key.
-
Move the serverpfx.pem file to /etc/ssl/certs/
-
Update the permissions: sudo chmod 644 /etc/ssl/certs/serverpfx.pem
-
Restart the Apache service: sudo service apache2 restart
In case, you wish us to make the serverpfx.pem file, write back to us on support@intranetssl.net
No Comments Yet.
In what format you issue the Intranet SSL Certificates ?
We issue SecureNT Intranet SSL certificate in PEM format with .cer extension.
The PEM format is the most common format used for certificates. Extensions used for PEM certificates are cer, crt, and pem. They are Base64 encoded ASCII files.
PEM formatted certificates contain the “Begin Certificate/End Certificate” statements.
The DER format is the binary form of the certificate. DER formatted certificates do not contain the “BEGIN CERTIFICATE/END CERTIFICATE” statements.
DER formatted certificates most often use the ‘.der’ extension. Root Certificates on Resource page are in DER format.
In case, you want them in PEM format send Email to support@intranetssl.net
No Comments Yet.
Is it compulsory to provide CSR to get Intranet SSL ?
Not necessary.
Just fill-up the form and we will generate the CSR (called Auto-CSR). And we will send the SSL Certificate along with the private key.
Tagged In
No Comments Yet.
What are the main features of SecureNT Intranet SSL Certificates ?
- Secure localhost, Server Name, Internal IP Address, Internal Domain, Sub-domain including Wildcard domain e.g., *.company.local
- Secure multiple servers using SAN values
- Certificates valid up to 10 years
- Install the same certificate on unlimited servers
- The certificate is issued with SecureNT Intranet Root & Intranet Intermediate CA chain. They are to be installed on each client’s machine.
- Fast Issuance, usually less than 24 hours
- Fast Expert Customer Support
- Automatic renewal reminders and early renewal options
- 30-day free certificate for Single Domain. 7-day free certificate for Multi-domain and Wildcard.
- Certificates with Custom Root CA in the name of your Organization are available
- Client Authentication Certificates for Web-based Applications and Document Management Systems available
Tagged In
No Comments Yet.
While requesting Intranet SSL, should I generate CSR or just give certificate details ?
Good question.
It is always recommended to generate CSR on your web server and share with us. This is because the private key generated during the CSR generation remains on your server, within your premises.
On the other hand, if you give certificate details to us, we generate the CSR. It is called Auto-CSR. During this process, private key is generated on our machine. When we ship the Intranet SSL to you, we send the SSL certificate along with the private key. This method is slightly risky because the private key can be intercepted by someone when it is sent through email.
But generation of CSR for Intranet SSL poses some technical challenges. Reason is that modern browsers expect the CSR to have require SAN values correctly specified.
For example, if the Common Name is “abc.local” then the CN=abc.local and SAN value should be DNS=abc.local. But it is not easy to generate CSR with SAN values on Windows or Linux.
Another issue comes when the certificate is to be issued to an IP address. In this case SAN should have two values. They are DNS=[IP-address] and IP=[IP-Address].
If any of these SAN values are not specified while generating the CSR then browser gives 'Certificate not Trusted' error.
Of course, we have shared the steps to generate CSR with SAN values. Link is given below.
Tagged In
No Comments Yet.
How to get Intranet SSL from your website ?
This video shows step by step how to get SecureNT Intranet SSL from our website.

In case you wish to generate CSR and you want us to generate the Intranet SSL then keep following points in mind.
- While generating CSR for Intranet SSL you need to ensure that relevant SAN value is part of the CSR. If SAN value is missing then we will have to ask you to generate CSR again with required SAN values.
- While generating CSR for IP address you need to ensure that two SAN values are there in the CSR. They are DNS=
and IP= . This is explained in - How to generate correct CSR when IP address is in CN or SAN - Following FAQs explain how to generate CSR with SAN values in Windows and Linux Servers.
How to generate correct CSR when IP address is in CN or SAN
How to Create CSR with SAN Values Using OpenSSL
In case you find it difficult to generate the CSR on your web server, don't worry. We will generate the Auto-CSR and we will send you the Intranet SSL in PFX format with Private Key.
Tagged In
No Comments Yet.
How to create CSR with SAN on Windows Data Center Edition ?
To generate a CSR (Certificate Signing Request) with SAN (Subject Alternative Names) on Windows Server 2022 Datacenter Edition, the most straightforward and flexible method is using PowerShell with a custom INF file and the Certreq utility.
Here’s a step-by-step guide:
✅ Step 1: Create an INF File (Certificate Request File)
To create a CSR with CN with 2 DNS SANs and 2 IP SANs .Create a new text file named request.inf and paste the following content into it:
[Version]
Signature="$Windows NT$"
[NewRequest]
Subject = "CN=<CN>; O=<Org Name>; L=<City>; S=<state>; C=<2 Digit Country Code>"
KeySpec = 1
KeyLength = 2048
Exportable = TRUE
MachineKeySet = TRUE
SMIME = FALSE
PrivateKeyArchive = FALSE
UserProtected = FALSE
UseExistingKeySet = FALSE
ProviderName = "Microsoft RSA SChannel Cryptographic Provider"
ProviderType = 12
RequestType = PKCS10
KeyUsage = 0xa0
[Extensions]
2.5.29.17 = "{text}"
_continue_ = "dns=<CN>&"
_continue_ = "dns=<SAN-1>&"
_continue_ = "dns=<SAN-2>&"
_continue_ = "dns=<IP-1>&"
_continue_ = "dns=<IP-2>&"
_continue_ = "ip=<IP-1>&"
_continue_ = "ip=<IP-2>"
[RequestAttributes]
CertificateTemplate = WebServerCustomize these fields:
CN=Your primary domain name e.g., *.server.local Under [Extensions] → List all DNS SANs (dns=SAN) and all IP SANs with (dns=IP-address) and (ip=IP-address) separated by "&"
Add or remove SANs as needed
✅ Step 2: Generate the CSR Using certreq
Open PowerShell as Administrator and run:
certreq -new request.inf server.csrThis creates a CSR file named server.csr which you can submit to SecureNT.
✅ Step 3: Submit CSR to CA
If you are using a private CA (SecureNT), upload the CSR as part of your certificate request.
✅ Step 4: Install the SSL Certificate
After receiving the signed certificate (.cer or .crt), install it with:
certreq -accept server.cerTagged In
No Comments Yet.
How to encrypt On-Premise SharePoint traffic with Intranet SSL ?
Microsoft recommends using HTTPS for all SharePoint web applications to ensure secure communication over port 443, as outlined in their official documentation.
Step-by-Step: Encrypt SharePoint with SecureNT Intranet SSL
Follow these steps to secure your SharePoint 2016, 2019, or Subscription Edition deployment with SecureNT Intranet SSL.
1. Generate a Certificate Signing Request (CSR)
Following steps are applicable for all versions of IIS. Windows Server should be domain joined.
- Open the MMC console and add the Certificate snap-in to it as Local Computer. Right Click Personal node on the left and Select All Tasks –>Advanced Operations –> Create Custom Request.
- Choose Proceed without enrollment policy and Click Next. Choose No Template Legacy Key for compatibility reasons. Use PKCS#10.
- Click Next and click Properties. Give a friendly name for the certificate (e.g., SharePoint SSL) and a description. Ensure that you hit Apply as soon as you are done with the tab.
- Click on Subject tab and add all the hostnames under “Alternative Name“ e.g., sharepoint.company.local. Under Subject Name, enter the Common Name (CN) e.g., sharepoint.company.local, Organization (O), City (L), State (S), and 2 letter Country (C) code values. Click Apply.
- Under the Extensions tab, expand Extended Key Usage (application policies) and select Server Authentication and Client Authentication. Click Apply.
- Under the Private Key tab, set the Key size to 2048 (or 4096) and SHA256 algorithm under options. Tick Make Private Key exportable. Select Exchange as the Key type. Click Apply. Click OK.
- Select a location to save the file. Choose the file format as Base 64. Click Finish.
CSR is generated with SAN values.
Note: If you don't wish to generate CSR then you can simply fill in all certificate details e.g., Domain = Common Name (e.g., sharepoint.company.local), Organization Name, City, State, and Country. And Auto-CSR will be generated by us.
2. Obtain a SecureNT Intranet SSL Certificate
- Visit intranetssl.net. Request Free or Paid certificate.
- Upload the CSR to the Certificate request form.
- Download the signed certificate (
.cerformat) and CA chain bundle.
SecureNT certificates are X.509-compliant and trusted across your domain once the SecureNT Root CA is deployed.
3. Install the Certificate in IIS
- In IIS Manager, go to Server Certificates > Complete Certificate Request.
- Upload the
.cerfile and assign a friendly name. - Under your SharePoint web app, go to Bindings, add an HTTPS binding on port 443, and select the installed certificate.
4. Configure SharePoint for HTTPS
- In SharePoint Central Administration, update Alternate Access Mappings (AAMs) to use
https://. - Optionally, redirect HTTP traffic to HTTPS using IIS rewrite rules or network policies.
5. Deploy the SecureNT Root CA
- Two SecureNT CA certificates (root and intermediate) are sent along with the certificate.
- Distribute it via Group Policy under Trusted Root Certification Authorities. Here are the steps.
- Ensure all domain-joined devices trust the CA.
No Comments Yet.
What is client authentication in SSL/TLS ?
Client authentication is a security mechanism where the server verifies the identity of the client using an SSL certificate. It is commonly implemented using mutual TLS (mTLS), where both client and server authenticate each other before a connection is established.
Tagged In
No Comments Yet.
Does SecureNT Intranet SSL support mutual TLS (mTLS) ?
Yes. SecureNT Intranet SSL fully supports mutual TLS (mTLS), where both the client and server present and validate SSL certificates during the connection process.
No Comments Yet.
Do client devices need to trust SecureNT certificates ?
Yes. Since SecureNT is a private CA, the SecureNT root certificate must be installed on client devices, servers, or systems that need to trust the certificates.
This is standard practice for intranet and enterprise environments.
No Comments Yet.
Categories
Tags