General FAQ
For protecting multiple IP addresses, Wildcard SSL is not possible. One has to buy either Single Domain or Multi-Domain.
Say, you wish to secure, say an entire range of IP addresses from 192.168.52.1 to 192.168.51.255.
For this, is it possible to buy Wildcard SSL for 192.168.52.*?
Unfortunately, no. That’s not possible.
For securing this IP address range, either one can buy Single Domain for each IP or Multi-Domain Intranet SSL certificate with required IP address in SAN values.
Single Domain SSL Certificate secures an Intranet Server’s Local Host Name, Server Name, internal/public IP Address, or Web page URL using Secure HTTPS protocol.
SecureNT Intranet SSL Certificate – Single Domain secures an Intranet Server’s Local Host Name, Server Name, internal/public IP Address, or Web page URL using Secure HTTPS protocol.
Certificates are valid for a period ranging from 1 to 10 years. One can install the certificate on unlimited servers. We offer a 90-day Free Single Domain Certificate.
Leave a Reply
Technical Information
For protecting multiple IP addresses, Wildcard SSL is not possible. One has to buy either Single Domain or Multi-Domain.
Say, you wish to secure, say an entire range of IP addresses from 192.168.52.1 to 192.168.51.255.
For this, is it possible to buy Wildcard SSL for 192.168.52.*?
Unfortunately, no. That’s not possible.
For securing this IP address range, either one can buy Single Domain for each IP or Multi-Domain Intranet SSL certificate with required IP address in SAN values.
Leave a Reply
This FAQ shows how to create a Certificate Signing Request (CSR) file with SAN values on the webserver using OpenSSL.
For creating CSR with SAN values (X.509 v3 Extension) it’s important to create a configuration file with the required certificate details. Execute following command in openssl.
openssl req -newkey rsa:2048 -nodes -keyout pvtkey.cer -config config.cnf -out csr.txt -utf8
It will create a Private key (pvtkey.cer) and CSR file (csr.txt).
Sample Configuration file (config.cnf)
[req]
prompt = no
distinguished_name = dn
req_extensions = ext
[dn]
CN = 192.168.2.23
O = Abc Corporation
L = Sydney
ST = New South Walse
C = AU
[ext]
subjectAltName = @alt_names
[alt_names]
IP.1 = 192.168.2.23
IP.2 = 10.12.4.122
DNS.1 = 192.168.2.23
DNS.2 = 10.12.4.22
DNS.3 = sms.abc.local
DNS.4 = localhost
It will generate CSR with CN=192.168.2.23 and 3 SAN values: 10.12.4.122, sms.abc.local and localhost.
Notice that when IP address is there in CN or SAN, we need to put its value against both IP Address and DNS. For others (URL, Servername etc) only DNS value is required.
Leave a Reply
How to generate correct CSR when the IP address is in CN or SAN? Please ensure that the IP address is mentioned in the SAN extension as IP Address and DNS Name.
When an internal/external IP Address is part of Common Name (CN) or Subject Alternative Name (SAN) care needs to be taken while generating the CSR.
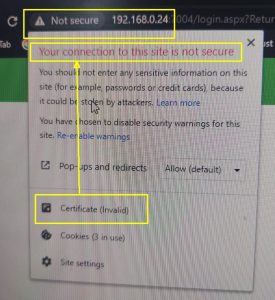
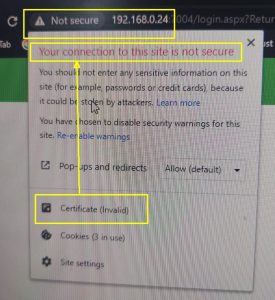
If not done correctly then the latest browsers like Chrome and Edge give an error – “Your connection to this site is not secure.” Note that deprecated Microsoft Internet Explorer does not give any error in this case.
To avoid this problem please ensure that the IP address is mentioned in the SAN extension as DNS Name and IP Address.
A sample configuration file is shown below for Multi-domain Certificate with 1+3 SAN values, where CN has IP-Address-1 and SAN values are IP-Address-2, SAN-1, and SAN-2.
———
[req]
prompt = no
distinguished_name = dn
req_extensions = ext
[dn]
CN = IP-Address-1
O = Org Name
L = Location/City
ST = State/Province
C = 2 digit code
[ext]
subjectAltName = @alt_names
[alt_names]
IP.1 = IP-Address-1
IP.2 = IP-Address-2
DNS.1 = IP-Address-1
DNS.2 = IP-Address-2
DNS.3 = SAN-1
DNS.4 = SAN-2
———
Leave a Reply
Secure localhost, Server Name, Internal IP Address, Internal Domain, Sub-domain including Wildcard domain e.g., *.company.local Secure multiple servers using SAN values. Certificates valid up to 10 years. Install the same certificate on unlimited servers.
- Secure localhost, Server Name, Internal IP Address, Internal Domain, Sub-domain including Wildcard domain e.g., *.company.local
- Secure multiple servers using SAN values
- Certificates valid up to 10 years
- Install the same certificate on unlimited servers
- The certificate is issued with SecureNT Intranet Root & Intranet Intermediate CA chain. They are to be installed on each client’s machine.
- Fast Issuance, usually less than 24 hours
- Fast Expert Customer Support
- Automatic renewal reminders and early renewal options
- 30-day free certificate for Single Domain. 7-day free certificate for Multi-domain and Wildcard.
- Certificates with Custom Root CA in the name of your Organization are available
- Client Authentication Certificates for Web-based Applications and Document Management Systems available
Leave a Reply
It is recommended to use CSR while requesting Intranet SSL. When you give certificate details then private key is sent over email. This may pose security risk. But generation of CSR with SAN values is not easy. So, steps are shared for the same.
Good question.
It is always recommended to generate CSR on your web server and share with us. This is because the private key generated during the CSR generation remains on your server, within your premises.
On the other hand, if you give certificate details to us, we generate the CSR. It is called Auto-CSR. During this process, private key is generated on our machine. When we ship the Intranet SSL to you, we send the SSL certificate along with the private key. This method is slightly risky because the private key can be intercepted by someone when it is sent through email.
But generation of CSR for Intranet SSL poses some technical challenges. Reason is that modern browsers expect the CSR to have require SAN values correctly specified.
For example, if the Common Name is “abc.local” then the CN=abc.local and SAN value should be DNS=abc.local. But it is not easy to generate CSR with SAN values on Windows or Linux.
Another issue comes when the certificate is to be issued to an IP address. In this case SAN should have two values. They are DNS=[IP-address] and IP=[IP-Address].
If any of these SAN values are not specified while generating the CSR then browser gives ‘Certificate not Trusted’ error.
Of course, we have shared the steps to generate CSR with SAN values. Link is given below.
https://intranetssl.net/ufaq/how-to-create-the-csr-with-san-in-windows-iis/
https://intranetssl.net/ufaq/how-to-create-csr-with-san-values-using-openssl/
Leave a Reply
Installation FAQ
How to generate correct CSR when the IP address is in CN or SAN? Please ensure that the IP address is mentioned in the SAN extension as IP Address and DNS Name.
When an internal/external IP Address is part of Common Name (CN) or Subject Alternative Name (SAN) care needs to be taken while generating the CSR.
If not done correctly then the latest browsers like Chrome and Edge give an error – “Your connection to this site is not secure.” Note that deprecated Microsoft Internet Explorer does not give any error in this case.
To avoid this problem please ensure that the IP address is mentioned in the SAN extension as DNS Name and IP Address.
A sample configuration file is shown below for Multi-domain Certificate with 1+3 SAN values, where CN has IP-Address-1 and SAN values are IP-Address-2, SAN-1, and SAN-2.
———
[req]
prompt = no
distinguished_name = dn
req_extensions = ext
[dn]
CN = IP-Address-1
O = Org Name
L = Location/City
ST = State/Province
C = 2 digit code
[ext]
subjectAltName = @alt_names
[alt_names]
IP.1 = IP-Address-1
IP.2 = IP-Address-2
DNS.1 = IP-Address-1
DNS.2 = IP-Address-2
DNS.3 = SAN-1
DNS.4 = SAN-2
———
Leave a Reply
It is recommended to use CSR while requesting Intranet SSL. When you give certificate details then private key is sent over email. This may pose security risk. But generation of CSR with SAN values is not easy. So, steps are shared for the same.
Good question.
It is always recommended to generate CSR on your web server and share with us. This is because the private key generated during the CSR generation remains on your server, within your premises.
On the other hand, if you give certificate details to us, we generate the CSR. It is called Auto-CSR. During this process, private key is generated on our machine. When we ship the Intranet SSL to you, we send the SSL certificate along with the private key. This method is slightly risky because the private key can be intercepted by someone when it is sent through email.
But generation of CSR for Intranet SSL poses some technical challenges. Reason is that modern browsers expect the CSR to have require SAN values correctly specified.
For example, if the Common Name is “abc.local” then the CN=abc.local and SAN value should be DNS=abc.local. But it is not easy to generate CSR with SAN values on Windows or Linux.
Another issue comes when the certificate is to be issued to an IP address. In this case SAN should have two values. They are DNS=[IP-address] and IP=[IP-Address].
If any of these SAN values are not specified while generating the CSR then browser gives ‘Certificate not Trusted’ error.
Of course, we have shared the steps to generate CSR with SAN values. Link is given below.
https://intranetssl.net/ufaq/how-to-create-the-csr-with-san-in-windows-iis/
https://intranetssl.net/ufaq/how-to-create-csr-with-san-values-using-openssl/

Leave a Reply